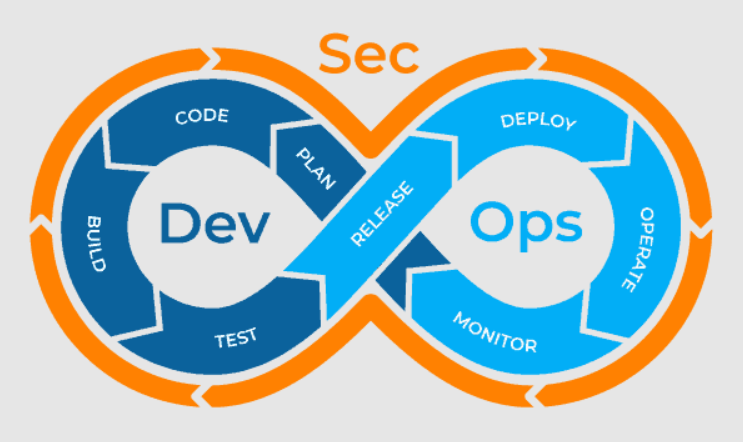
When there’s a perfect opportunity to fortify the app from the inside out against future threats, DevSecOps is the method of incorporating protection into the entire application development process. Since several companies create applications regularly to meet consumer or business partner demands, DevSecOps is gaining huge momentum. One such reliable source is https://sonraisecurity.com/who-we-serve/devsecops/.
According to Market Research, the global DevSecOps market is projected to expand from $1.47 billion in 2018 to $13.63 billion by 2026, owing to the constant rise and perniciousness of cybersecurity threats. A broad range of DevSecOps tools makes up the market.
Open Source Security Toolsets:
Integrating security monitoring in the software development and implementation pipeline is not a single project—it’s a continuous endeavor, whether you call it “shifting left”, modern app dev security, or DevSecOps.
Open-source software can be extremely beneficial. They are not only a good way to get started, enabling companies and DevSecOps teams to gain experience with incorporating security tooling into the workflow, but they can also assist companies in establishing the framework they need to integrate security into growth.
- OWASP Threat Dragon Threat Modeling
The first security phase should be threat modeling, as it informs application design and can give developers an idea of what security threats can affect their application. OWASP Threat Dragon is an open-source threat modeling platform for Windows, macOS, and Linux that can be accessed through a web application or an installable version.
The downside of OWASP Threat Dragon is that it is heavily reliant on GitHub, so if you use a different repository system, you’ll need to find another tool.
- Application Security Testing (Static) (SAST)
SonarQube is a community-supported open-source source-code review platform that also offers paid levels for businesses. Although OWASP maintains a list of source-code review tools, many of which are open-source projects, most of them only support a few, if any, programming languages, and many of them are out of date.
Other options:
Bandit is a Python security linter that finds vulnerabilities using Abstract Syntax Trees (ASTs). Graudit is a simple static tool that supports over 20 languages.
- Analysis of Software Composition
OWASP Dependency Track is a project run by the Open Web Application Security Project.
Dependency Track generates a software bill of materials and tracks the usage of software components in the application portfolio to determine the danger they pose. With built-in support for the major package-management ecosystems, including JavaScript (NPM),.NET (NuGet), Python (PyPI), Java (Maven), and Gems(Ruby), the program detects known vulnerabilities in modules, license risk, and out-of-date libraries.
Various options:
Retire.js: Detects JavaScript components that are vulnerable. The open-source SCA tool SonaType Nexus Open Source supports a dozen different component ecosystems.
- Threat Playbook for Security Testing
Though Threat Playbook is first and foremost a threat modeling tool (see No. 1), it also converts threat models into code that can be used as security test cases in a continuous integration/continuous deployment (CI/CD) environment. The tool’s collaboration features stand out, and it’s designed to fit into a DevOps tech pipeline.
- Control of Degradation: Deepfence Threat Mapper Community Edition
When staging apps for testing, DevOps teams must ensure that no errors have crept into their configuration files or infrastructure, causing them to degrade. Threat Mapper assists teams by allowing them to imagine their cloud infrastructure and managing vulnerabilities across all infrastructure components. To automate coverage, the app integrates with Kubernetes.
Other options:
Container images can be inspected, analyzed, and certified using Anchor Engine.
Clair: Static study of Docker containerized applications
- Regression in Security
Faraday DevOps teams will move from threat models to a red-team approach to regression testing with Faraday. Faraday automates testing by integrating with a range of vulnerability evaluation and penetration testing methods.
Other options:
ArcherySec is a well-known open-source platform for assessing and managing vulnerabilities. OWASP’s DefectDojo project automates vulnerability evaluation and management.
Final Thoughts
Open-source software can meet a variety of needs, depending on how many security-focused developers are on the DevOps team. Commercial security tools or commercial versions of open-source products are needed for teams that need assistance, deeper coverage of threats and vulnerabilities, or the capacity to scale to thousands of systems.