Data safety has been the latest craze in the digital world. The importance of personal data and its breach was brought out in the open by Mark Zuckerberg’s testimony in front of the US Senate for the Facebook–Cambridge Analytica data breach. While there are many technicalities to this whole event the major takeaway was that the major tech giants have been using the personal data of the consumers and selling it to the highest bidder primarily for sponsorship or even channeling public opinion to win elections.
There has been much speculation about rigging election results but upon keen observation in your newsfeed in any social media platform would notice that the sponsored content or the advertisements are usually aligned with the type of content that browse or look into. Even though these little inputs seem harmless on the face, they have a deep impact on the behavior and psyche of the user. What is more alarming is that even our bank details are not safe because of such data breaches.
Data Safety:
Many governments, especially the European ones, have given data safety quite a serious consideration. Any kind of new induction of a customer into any organization is bound by various rules and regulations like the GDPR where the customers’ approval is specifically requested for handling their data along with retaining them.
A data breach has been of major concern for almost every corporate organization all over the world because it paves the way for a security threat to the company’s confidential and sensitive data. In recent times, Cognizant’s Ransomware attack has proven again the importance of data safety.
In the light of data security and safety, almost all of the major corporations are investing heavily in data management and retention. As a result, various types of tools and processes are implemented all through the company’s landscape to ensure that the relevant data is safe and secure. While many of the processes are in place to ensure there is no breach of data, one of the most important processes is enterprise content management.
Enterprise Content Management:
Even though content management is not directly linked to data security, it has an underlying implication of their safety. It is because content management directly deals with information publishing in any format whether digital or physical. Needless to mention, dealing with any kind of information is inherent in data safety. To answer the question asked at the very beginning of the discussion, one should first have an understanding of Enterprise Content Management.
You need to make sure that the information that you have collated is completely protected, such as with an offsite data protection facility, because without that protection – on both software and on paper – you are at risk of someone coming in and taking what’s not theirs.
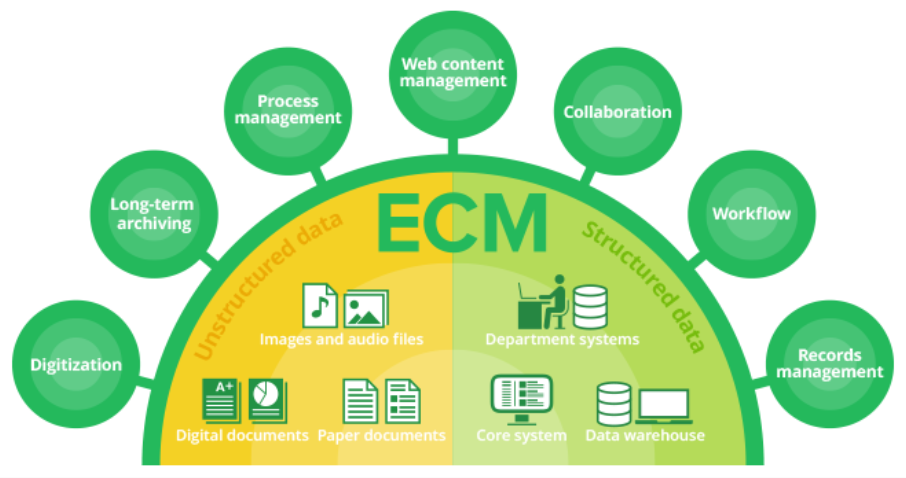
Enterprise Content Management, shortened as ECM can be considered as a specific branch of content management that is governed especially by timelines. Apart from the time-bound activities, Enterprise Content Management also enforces specific processes to create, approve, and distribute various kinds of information both in the digital and in the physical forms of publishing. Coming back to answer the question asked above, ECM kind of forms the stepping stone to data safety because they deal with the access rights to the documents and determine the audience for them. Read more about What Is Big Data and How Does it Impact You?
This practice is an important aspect of data privacy, where data and information are shared to only relevant audiences and unwanted access is not allowed for those documents. Another factor that makes ECM interesting is the inclusion of new items to the list of existing items and their seamless management. In most corporations, ECM is often combined with Digital Rights Management also known as DRM. What makes ECM different from its predecessor of content management is the recognition of and strict adherence to the procedures and processes of an enterprise for which the document is being created.
Scope of ECM:
Enterprise Content Management spans three major areas:
- Digital archiving of the documents starting from capturing searching and networking of the documents
- Managing the documents from their creation to their closure
- Monitoring the workflow involved in document creation and maintenance
While the above three areas form the foundation of ECM, tackling the challenges in the use and preservation of an organization’s internal information regularly, especially the unstructured ones can be easily deemed as the pillar on which ECM stands with its spine straight.
The most common form of ECM solutions is usually the B2E (Business to Employee) system. Just like any other technological advancement, ECM is also evolving at a rapid pace. Any content when being checked in or checked out has a system to generate the respective metadata to allow better audit trailing information.
This information about document use has been proven quite beneficial in understanding the management of data safety because as the system gets such information it automatically aligns mechanisms for new filtering methods, searching and routing for pathways, and undergoes many more functionalities that prove to be handy in data safety and security.
Manifestations of ECM:
It is quite difficult to point out the existence of a good ECM in any corporate program because it is supposed to stay invisible and be in the background working seamlessly to ensure that contents and documents are managed without any hiccups. This special characteristic of ECM can be easily used as its manifestation.
Any program or project that has impeccable documentation management and handling of unstructured internal data is a fine example of perfect ECM.
Information management often becomes a headache for large corporations. It is here that the ECM comes into play and takes away the hassles associated with information and in turn relevant document management. ECM not only helps in cost reduction for document management but also streamlines data search functionality largely. ECM allows employees of any organization to have easy access to the respective information without much hassles and issues.
Conclusion:
In continuation of the discussion about data safety, ECM provides a great amount of coverage against data breaches. However, it is not a full-proof safety net against data security. For reaching a stage of absolute data security, both consumers and corporate should have an ethical mindset leaving behind the money-saving and money-making mentalities in place of the services availed or rendered respectively.